Configure the Security Properties
POTENTIAL SECURITY BREACH
The Broker tab on the Forms of MQTT Broker items includes a Security section. Use the section to specify whether the connection to the broker is secured using the Transport Layer Security (TLS) protocol. For more information, see Transport Layer Security (TLS).
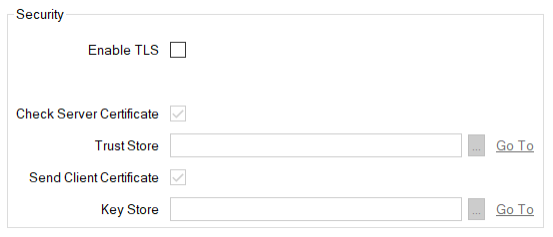
- Enable TLS—Select this check box for Geo SCADA Expert to make a secure connection to the MQTT broker using the TLS protocol.
Clear the check box (the default) if the connection between Geo SCADA Expert and the broker is not secured. The rest of the fields within the Security section are 'grayed out' and unavailable for use.
- Check Server Certificate—Select this check box for Geo SCADA Expert (the client) to authenticate the broker (the server). This authentication process checks that the broker to which Geo SCADA Expert connects has a trusted certificate. The broker is represented in the database by this MQTT Broker database item.
- Trust Store—Specify the trusted certificates for the broker (the server). These certificates are used to authenticate the broker. Geo SCADA Expert only authenticates the broker when the Check Server Certificate option is enabled.
The MQTT driver supports only X.509 certificates in the PEM format (see Which SSL Certificate File Types does my Driver Support?).
If the broker's certificate is issued by a certificate authority (CA), add the certificate authority's root certificate. If the broker's certificate is self-signed, add a copy of the self-signed certificate.
In each case, you use an SSL Certificate database item to import and store the certificate in the database (see Use SSL Certificates for Driver Communications). You use the Trust Store field to specify this SSL Certificate database item. Use the browse button to display a Reference browse window and then select the required entry from the window.
- Send Client Certificate—Select this check box if the broker (the server) is to authenticate Geo SCADA Expert (the client). During the TLS handshake, the broker can request Geo SCADA Expert's (the client's) certificate and then use this certificate to authenticate Geo SCADA Expert against the broker's trusted certificates.
- Key Store—Specify the client certificate for the Geo SCADA Expert system. This certificate is used by the broker (the server) to authenticate Geo SCADA Expert (the client).
The MQTT driver supports only X.509 certificates in the PEM format, and all types of private keys in the PEM format (see Which SSL Certificate File Types does my Driver Support?).
If you are using a certificate authority to issue the certificate, add the end-entity certificate and private key, along with any intermediate certificates that are required to verify the certificate. The broker should trust the certificate authority's root certificate. If you are using a self-signed certificate, add the self-signed certificate and private key. The broker should trust this individual certificate.
In each case, you use an SSL Certificate and Key database item to import and store the client certificates and the private key for the end-entity certificate in the database (see Use SSL Certificates for Driver Communications). You use the Key Store field to specify this SSL Certificate and Key database item.
For compliance with the IEC 62351-3 standard, mutual authentication is required. Therefore, you need to enable both the Check Server Certificate and Send Client Certificate check boxes. You must also configure the MQTT broker to authenticate Geo SCADA Expert and to trust the certificate that is configured in the Key Store field.
LOSS of communication
Further Information